Edited
Remote Access
Last minute hack, started Sun, 11:55...
Just looking around:
1) Come to venue, see Wi-Fi password
2) $ ifconfig => my IP, e.g. 192.168.0.23
3) $ nmap 192.168.0.0-255 -p 80 => e.g. 192.168.0.42 looks like an oven
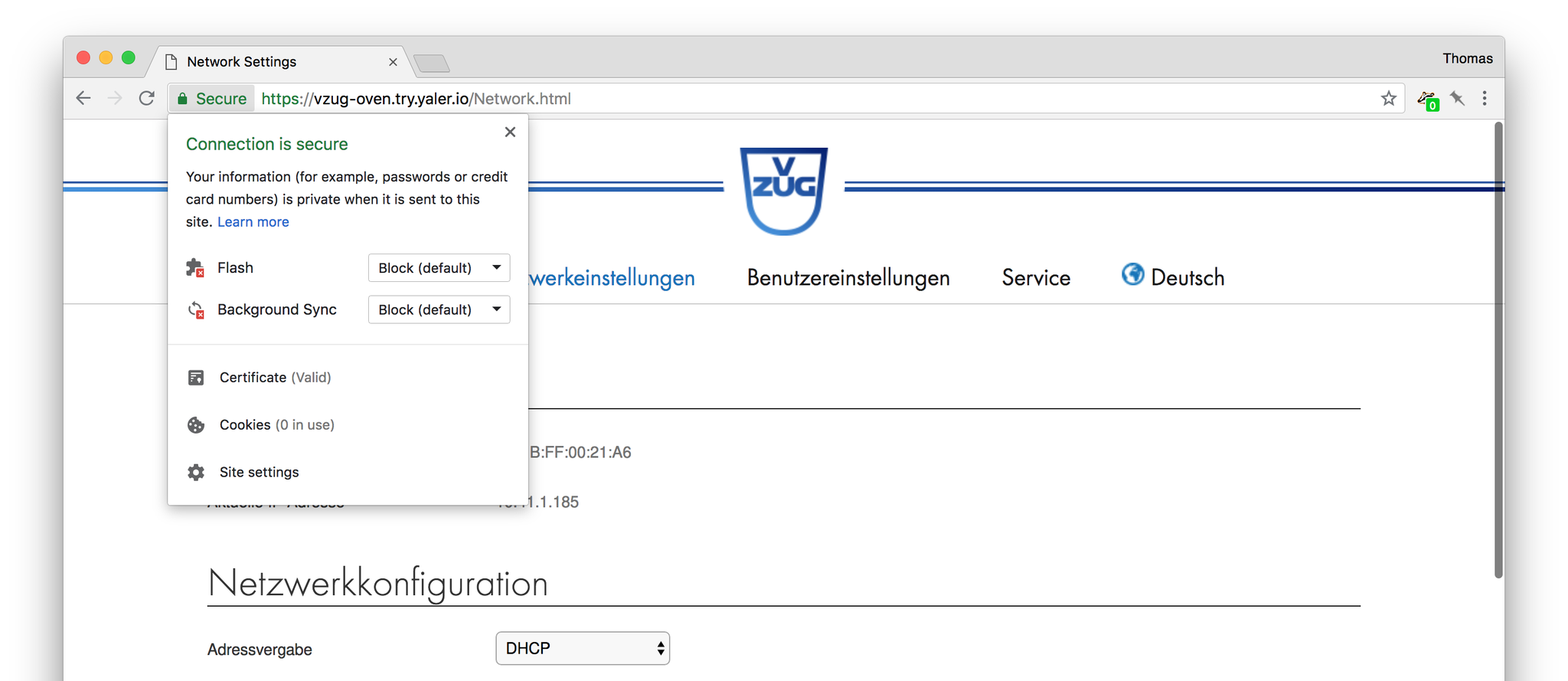
4) Access 192.168.0.42/Network.html => Sicherheitseinstellungen => set user "admin", password "hacked"
Let's add SSL/TLS and remote access:
5) https://yaler.net/ => RELAY_DOMAIN
6) https://yaler.net/macos => ./yalertunnel installed (would run right on the oven MCU in a real deployment)
7) $ ./yalertunnel server 192.168.0.42:80 ssl:try.yaler.io:443 RELAY_DOMAIN -min-listeners 8
8) Access (from everywhere) https://RELAY_DOMAIN.try.yaler.io/
9) E.g. on your phone https://chart.googleapis.com/chart?cht=qr&chs=150x150&choe=UTF-8&chld=H&chl=https://RELAY_DOMAIN.try.yaler.io/
(Full disclosure: I'm a founder of Yaler)
Event finished
Joined the team
First post View challenge

